How useful are the Intel Customer Scripts (“CScripts”) for debugging system issues?
Bringing up a new board design based on Intel processors can be a daunting task. Fortunately, Intel® provides the CScripts library to its customers, which is extremely useful when debugging hardware/firmware/software issues. The CScripts routines provide a range of capabilities, from basic state dump (register and memory dumps) to error injection/logging and sideband-enabled postmortem access.
The beauty of the CScripts is that they are a set of canned routines which can be run independent of the level of expertise of the user, and independent of the complexity and source of the problem they are being used to troubleshoot. In the first instance, an engineer inexperienced in the depths of Intel Architecture (IA) can nonetheless run the canned routines, and hand the results in a “standard” output format to Intel for later post-mortem analysis. Or a person with deep knowledge of IA can look for “breadcrumbs” and identify what is most likely the root cause to the designer – either Intel itself, the hardware board designers, the driver firmware supplier, the BIOS supplier, and so on.
In the second instance, the OEM or ODM may have no idea what may be causing the issue, but the root cause is buried away in some obscure register which might be obvious only to its supplier who has access to the source code – seeing the CScripts output of this register in a predefined format/layout may result in an “aha” moment.
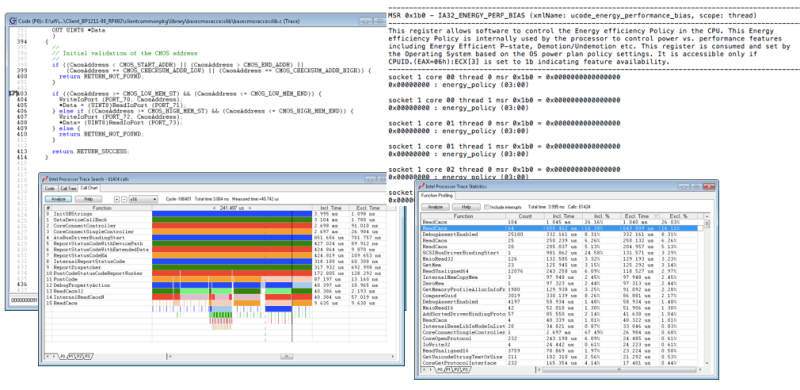
These canned routines include what Intel calls “The Big Four” analysis routines: sysDump(), sysError(), sysInfo() and sysTopo(). And there are numerous modules and functions therein, such as crashdump, which can fetch a subset of system data even in the event of a three-strike timeout. And the Python environment supporting the CScripts lends itself to whatever customization is needed to extract the needed forensics. There are literally an infinite number of ways to use the CScripts to identify root cause.
Combined with powerful source-level debug and trace capabilities, such as is found in the SourcePoint JTAG-assisted debugger, or with in-situ forensics access, as with ScanWorks Embedded Diagnostics (SED), these CScripts are a valuable addition to any engineer’s toolkit.
For more information on the CScripts, and SourcePoint’s support for them, check out our eBook here (note: requires registration).